Are you prepared for the remote work reality

In the days leading up to the March 13, 2020 declaration of national emergency related to Coronavirus (“COVID-19”), many businesses began taking steps to assure that their workforce could continue operations remotely. Since then, these steps have gone into overdrive as more and more employees and contractors are being discouraged (or prohibited) from situations that involve human-to-human physical contact. Businesses that have not embraced or prepared for this new “normal” may be challenged with additional risk exposure related to remote operations, as well as complications that may arise when bad actors seek to take advantage of public fear/disaster scenarios.
Here are some potential trouble spots:
Lack of internal policies and procedures — businesses that have never created formal policies may find it difficult to coordinate and respond to external threats and potential data security events. Because security events tend to move quickly, delays in management response may result in larger than necessary losses (data, business, cash, etc.).
Lack of IT infrastructure and expertise — businesses that cannot access relevant expertise (especially during periods of increased demand) run the risk of their technical demands not keeping up with a rapidly evolving environment. For those owners not accustomed to a purely remote experience, this lack of access may mean extended downtime (loss of business/revenue) and/or extended windows where system vulnerabilities expose proprietary data to bad actors.
Lack of training and awareness — non-native users who are now forced to access company data from a remote platform may not be familiar with proper protocols necessary (both from a system and a hardware perspective) to maintain adequate safeguards over both data and access to the internal network. Potential avenues include traditional “hacking”, phishing, spoofing, ransomware, malware, password theft, or other points of entry made vulnerable due to lack of controls or lack of compliance with existing controls.
Human nature — in situations of high panic and incomplete information, the first viable source becomes the most reliable source almost reflexively. Bad actors understand this and are quite skilled at creating vehicles that prey on our need to make sense of events. These “social engineering” tricks look and feel like reputable information and prompt actions which, without diligence, can compromise secure systems.
Companies that find themselves somewhat unprepared should consider the following tips and advice for navigating these challenging times:
- If you are seeking technical expertise, do your diligence and find a reputable IT professional. Now is not the time to go discount — you are entrusting your and your clients’ data to this person. Do not get taken advantage of. Ditto for applications and software that you will be told “you have to have” as you embark on a remote strategy.
- Develop and implement an internally visible and centralized plan for the inevitable technology problems that will arise. If you do not have a dedicated IT resource, make sure that your remote workers are getting assistance from an approved and reputable source that is familiar with your system and policies.
- Consider multi-factor authentication (MFA) if you have not already. MFA may consist of software or applications that send verifications to a known email address or phone number, or in some cases may be as simple as requiring personal verification of previously identified categories of requests over the phone.
- Watch for unauthorized work-arounds as these may be indicative of system or process vulnerabilities or may create vulnerabilities to outside parties.
- Your network speed may get slower due to increased usage — BY EVERYONE. Depending on your provider, the speed and bandwidth accessible to your company may be affected by the overall increase in traffic. This phenomenon is no different than everyone realizing the highway will close at 4 p.m., so they all leave the office at 1 p.m. or 2 p.m. to avoid traffic. Factor this “traffic” in, and where possible, plan accordingly.
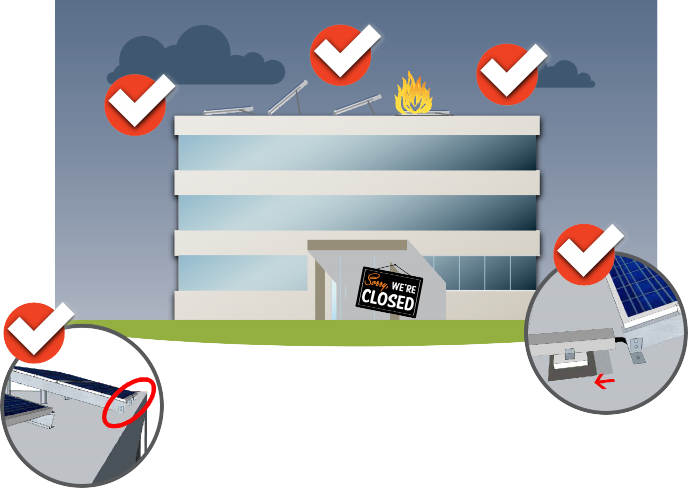
- Don’t forget your physical hardware and servers. For those that haven’t migrated to the cloud, consider your critical infrastructure and how it is physically protected (especially if located somewhere “closed until further notice”).
- Your staff may not have “work laptops” but may still need to access the company network on a device without the proper security setup. Train employees on minimum security requirements necessary for secure interface (VPN, firewalls, secure file exchange, avoiding “free wi-fi” in public spaces, etc.) and where needed consider follow-up measures (in-person configuration or retrieving/providing conforming hardware) to ensure compliance.
The governmental response to the COVID-19 pandemic will require most business to change the way they work, even if that change is temporary and regardless of whether they were prepared. Because this change is predictable, the threats related to that change are also somewhat predictable. The current environment not only means increased exposure to issues which traditionally confront users of technology to do business, but also increased numbers of companies who may be dealing with remote work for the first time on this level of scale. As you navigate your response to COVID-19, please make sure your systems and processes can withstand this new “normal.”
This material is provided for informational purposes only and does not provide any coverage or guarantee loss prevention. The examples in this material are provided as hypothetical and for illustration purposes only. The Hanover Insurance Company and its affiliates and subsidiaries (“The Hanover”) specifically disclaim any warranty or representation that acceptance of any recommendations contained herein will make any premises, or operation safe or in compliance with any law or regulation. By providing this information to you, The Hanover does not assume (and specifically disclaims) any duty, undertaking or responsibility to you. The decision to accept or implement any recommendation(s) or advice contained in this material must be made by you.
MAR LC 2020-161A
Are you prepared for the remote work reality
In the days leading up to the March 13, 2020 declaration of national emergency related to Coronavirus (“COVID-19”), many businesses began taking steps to assure that their workforce could continue operations remotely. Since then, these steps have gone into overdrive as more and more employees and contractors are being discouraged (or prohibited) from situations that involve human-to-human physical contact. Businesses that have not embraced or prepared for this new “normal” may be challenged with additional risk exposure related to remote operations, as well as complications that may arise when bad actors seek to take advantage of public fear/disaster scenarios.
Here are some potential trouble spots:
Lack of internal policies and procedures — businesses that have never created formal policies may find it difficult to coordinate and respond to external threats and potential data security events. Because security events tend to move quickly, delays in management response may result in larger than necessary losses (data, business, cash, etc.).
Lack of IT infrastructure and expertise — businesses that cannot access relevant expertise (especially during periods of increased demand) run the risk of their technical demands not keeping up with a rapidly evolving environment. For those owners not accustomed to a purely remote experience, this lack of access may mean extended downtime (loss of business/revenue) and/or extended windows where system vulnerabilities expose proprietary data to bad actors.
Lack of training and awareness — non-native users who are now forced to access company data from a remote platform may not be familiar with proper protocols necessary (both from a system and a hardware perspective) to maintain adequate safeguards over both data and access to the internal network. Potential avenues include traditional “hacking”, phishing, spoofing, ransomware, malware, password theft, or other points of entry made vulnerable due to lack of controls or lack of compliance with existing controls.
Human nature — in situations of high panic and incomplete information, the first viable source becomes the most reliable source almost reflexively. Bad actors understand this and are quite skilled at creating vehicles that prey on our need to make sense of events. These “social engineering” tricks look and feel like reputable information and prompt actions which, without diligence, can compromise secure systems.
Companies that find themselves somewhat unprepared should consider the following tips and advice for navigating these challenging times:
- If you are seeking technical expertise, do your diligence and find a reputable IT professional. Now is not the time to go discount — you are entrusting your and your clients’ data to this person. Do not get taken advantage of. Ditto for applications and software that you will be told “you have to have” as you embark on a remote strategy.
- Develop and implement an internally visible and centralized plan for the inevitable technology problems that will arise. If you do not have a dedicated IT resource, make sure that your remote workers are getting assistance from an approved and reputable source that is familiar with your system and policies.
- Consider multi-factor authentication (MFA) if you have not already. MFA may consist of software or applications that send verifications to a known email address or phone number, or in some cases may be as simple as requiring personal verification of previously identified categories of requests over the phone.
- Watch for unauthorized work-arounds as these may be indicative of system or process vulnerabilities or may create vulnerabilities to outside parties.
- Your network speed may get slower due to increased usage — BY EVERYONE. Depending on your provider, the speed and bandwidth accessible to your company may be affected by the overall increase in traffic. This phenomenon is no different than everyone realizing the highway will close at 4 p.m., so they all leave the office at 1 p.m. or 2 p.m. to avoid traffic. Factor this “traffic” in, and where possible, plan accordingly.
- Don’t forget your physical hardware and servers. For those that haven’t migrated to the cloud, consider your critical infrastructure and how it is physically protected (especially if located somewhere “closed until further notice”).
- Your staff may not have “work laptops” but may still need to access the company network on a device without the proper security setup. Train employees on minimum security requirements necessary for secure interface (VPN, firewalls, secure file exchange, avoiding “free wi-fi” in public spaces, etc.) and where needed consider follow-up measures (in-person configuration or retrieving/providing conforming hardware) to ensure compliance.
The governmental response to the COVID-19 pandemic will require most business to change the way they work, even if that change is temporary and regardless of whether they were prepared. Because this change is predictable, the threats related to that change are also somewhat predictable. The current environment not only means increased exposure to issues which traditionally confront users of technology to do business, but also increased numbers of companies who may be dealing with remote work for the first time on this level of scale. As you navigate your response to COVID-19, please make sure your systems and processes can withstand this new “normal.”
This material is provided for informational purposes only and does not provide any coverage or guarantee loss prevention. The examples in this material are provided as hypothetical and for illustration purposes only. The Hanover Insurance Company and its affiliates and subsidiaries (“The Hanover”) specifically disclaim any warranty or representation that acceptance of any recommendations contained herein will make any premises, or operation safe or in compliance with any law or regulation. By providing this information to you, The Hanover does not assume (and specifically disclaims) any duty, undertaking or responsibility to you. The decision to accept or implement any recommendation(s) or advice contained in this material must be made by you.
MAR LC 2020-161A
Are you prepared for the remote work reality
In the days leading up to the March 13, 2020 declaration of national emergency related to Coronavirus (“COVID-19”), many businesses began taking steps to assure that their workforce could continue operations remotely. Since then, these steps have gone into overdrive as more and more employees and contractors are being discouraged (or prohibited) from situations that involve human-to-human physical contact. Businesses that have not embraced or prepared for this new “normal” may be challenged with additional risk exposure related to remote operations, as well as complications that may arise when bad actors seek to take advantage of public fear/disaster scenarios.
Here are some potential trouble spots:
Lack of internal policies and procedures — businesses that have never created formal policies may find it difficult to coordinate and respond to external threats and potential data security events. Because security events tend to move quickly, delays in management response may result in larger than necessary losses (data, business, cash, etc.).
Lack of IT infrastructure and expertise — businesses that cannot access relevant expertise (especially during periods of increased demand) run the risk of their technical demands not keeping up with a rapidly evolving environment. For those owners not accustomed to a purely remote experience, this lack of access may mean extended downtime (loss of business/revenue) and/or extended windows where system vulnerabilities expose proprietary data to bad actors.
Lack of training and awareness — non-native users who are now forced to access company data from a remote platform may not be familiar with proper protocols necessary (both from a system and a hardware perspective) to maintain adequate safeguards over both data and access to the internal network. Potential avenues include traditional “hacking”, phishing, spoofing, ransomware, malware, password theft, or other points of entry made vulnerable due to lack of controls or lack of compliance with existing controls.
Human nature — in situations of high panic and incomplete information, the first viable source becomes the most reliable source almost reflexively. Bad actors understand this and are quite skilled at creating vehicles that prey on our need to make sense of events. These “social engineering” tricks look and feel like reputable information and prompt actions which, without diligence, can compromise secure systems.
Companies that find themselves somewhat unprepared should consider the following tips and advice for navigating these challenging times:
- If you are seeking technical expertise, do your diligence and find a reputable IT professional. Now is not the time to go discount — you are entrusting your and your clients’ data to this person. Do not get taken advantage of. Ditto for applications and software that you will be told “you have to have” as you embark on a remote strategy.
- Develop and implement an internally visible and centralized plan for the inevitable technology problems that will arise. If you do not have a dedicated IT resource, make sure that your remote workers are getting assistance from an approved and reputable source that is familiar with your system and policies.
- Consider multi-factor authentication (MFA) if you have not already. MFA may consist of software or applications that send verifications to a known email address or phone number, or in some cases may be as simple as requiring personal verification of previously identified categories of requests over the phone.
- Watch for unauthorized work-arounds as these may be indicative of system or process vulnerabilities or may create vulnerabilities to outside parties.
- Your network speed may get slower due to increased usage — BY EVERYONE. Depending on your provider, the speed and bandwidth accessible to your company may be affected by the overall increase in traffic. This phenomenon is no different than everyone realizing the highway will close at 4 p.m., so they all leave the office at 1 p.m. or 2 p.m. to avoid traffic. Factor this “traffic” in, and where possible, plan accordingly.
- Don’t forget your physical hardware and servers. For those that haven’t migrated to the cloud, consider your critical infrastructure and how it is physically protected (especially if located somewhere “closed until further notice”).
- Your staff may not have “work laptops” but may still need to access the company network on a device without the proper security setup. Train employees on minimum security requirements necessary for secure interface (VPN, firewalls, secure file exchange, avoiding “free wi-fi” in public spaces, etc.) and where needed consider follow-up measures (in-person configuration or retrieving/providing conforming hardware) to ensure compliance.
The governmental response to the COVID-19 pandemic will require most business to change the way they work, even if that change is temporary and regardless of whether they were prepared. Because this change is predictable, the threats related to that change are also somewhat predictable. The current environment not only means increased exposure to issues which traditionally confront users of technology to do business, but also increased numbers of companies who may be dealing with remote work for the first time on this level of scale. As you navigate your response to COVID-19, please make sure your systems and processes can withstand this new “normal.”
This material is provided for informational purposes only and does not provide any coverage or guarantee loss prevention. The examples in this material are provided as hypothetical and for illustration purposes only. The Hanover Insurance Company and its affiliates and subsidiaries (“The Hanover”) specifically disclaim any warranty or representation that acceptance of any recommendations contained herein will make any premises, or operation safe or in compliance with any law or regulation. By providing this information to you, The Hanover does not assume (and specifically disclaims) any duty, undertaking or responsibility to you. The decision to accept or implement any recommendation(s) or advice contained in this material must be made by you.
MAR LC 2020-161A
Are you prepared for the remote work reality
In the days leading up to the March 13, 2020 declaration of national emergency related to Coronavirus (“COVID-19”), many businesses began taking steps to assure that their workforce could continue operations remotely. Since then, these steps have gone into overdrive as more and more employees and contractors are being discouraged (or prohibited) from situations that involve human-to-human physical contact. Businesses that have not embraced or prepared for this new “normal” may be challenged with additional risk exposure related to remote operations, as well as complications that may arise when bad actors seek to take advantage of public fear/disaster scenarios.
Here are some potential trouble spots:
Lack of internal policies and procedures — businesses that have never created formal policies may find it difficult to coordinate and respond to external threats and potential data security events. Because security events tend to move quickly, delays in management response may result in larger than necessary losses (data, business, cash, etc.).
Lack of IT infrastructure and expertise — businesses that cannot access relevant expertise (especially during periods of increased demand) run the risk of their technical demands not keeping up with a rapidly evolving environment. For those owners not accustomed to a purely remote experience, this lack of access may mean extended downtime (loss of business/revenue) and/or extended windows where system vulnerabilities expose proprietary data to bad actors.
Lack of training and awareness — non-native users who are now forced to access company data from a remote platform may not be familiar with proper protocols necessary (both from a system and a hardware perspective) to maintain adequate safeguards over both data and access to the internal network. Potential avenues include traditional “hacking”, phishing, spoofing, ransomware, malware, password theft, or other points of entry made vulnerable due to lack of controls or lack of compliance with existing controls.
Human nature — in situations of high panic and incomplete information, the first viable source becomes the most reliable source almost reflexively. Bad actors understand this and are quite skilled at creating vehicles that prey on our need to make sense of events. These “social engineering” tricks look and feel like reputable information and prompt actions which, without diligence, can compromise secure systems.
Companies that find themselves somewhat unprepared should consider the following tips and advice for navigating these challenging times:
- If you are seeking technical expertise, do your diligence and find a reputable IT professional. Now is not the time to go discount — you are entrusting your and your clients’ data to this person. Do not get taken advantage of. Ditto for applications and software that you will be told “you have to have” as you embark on a remote strategy.
- Develop and implement an internally visible and centralized plan for the inevitable technology problems that will arise. If you do not have a dedicated IT resource, make sure that your remote workers are getting assistance from an approved and reputable source that is familiar with your system and policies.
- Consider multi-factor authentication (MFA) if you have not already. MFA may consist of software or applications that send verifications to a known email address or phone number, or in some cases may be as simple as requiring personal verification of previously identified categories of requests over the phone.
- Watch for unauthorized work-arounds as these may be indicative of system or process vulnerabilities or may create vulnerabilities to outside parties.
- Your network speed may get slower due to increased usage — BY EVERYONE. Depending on your provider, the speed and bandwidth accessible to your company may be affected by the overall increase in traffic. This phenomenon is no different than everyone realizing the highway will close at 4 p.m., so they all leave the office at 1 p.m. or 2 p.m. to avoid traffic. Factor this “traffic” in, and where possible, plan accordingly.
- Don’t forget your physical hardware and servers. For those that haven’t migrated to the cloud, consider your critical infrastructure and how it is physically protected (especially if located somewhere “closed until further notice”).
- Your staff may not have “work laptops” but may still need to access the company network on a device without the proper security setup. Train employees on minimum security requirements necessary for secure interface (VPN, firewalls, secure file exchange, avoiding “free wi-fi” in public spaces, etc.) and where needed consider follow-up measures (in-person configuration or retrieving/providing conforming hardware) to ensure compliance.
The governmental response to the COVID-19 pandemic will require most business to change the way they work, even if that change is temporary and regardless of whether they were prepared. Because this change is predictable, the threats related to that change are also somewhat predictable. The current environment not only means increased exposure to issues which traditionally confront users of technology to do business, but also increased numbers of companies who may be dealing with remote work for the first time on this level of scale. As you navigate your response to COVID-19, please make sure your systems and processes can withstand this new “normal.”
This material is provided for informational purposes only and does not provide any coverage or guarantee loss prevention. The examples in this material are provided as hypothetical and for illustration purposes only. The Hanover Insurance Company and its affiliates and subsidiaries (“The Hanover”) specifically disclaim any warranty or representation that acceptance of any recommendations contained herein will make any premises, or operation safe or in compliance with any law or regulation. By providing this information to you, The Hanover does not assume (and specifically disclaims) any duty, undertaking or responsibility to you. The decision to accept or implement any recommendation(s) or advice contained in this material must be made by you.
MAR LC 2020-161A